Which Statement Describes the Best Practice for Securing a Load
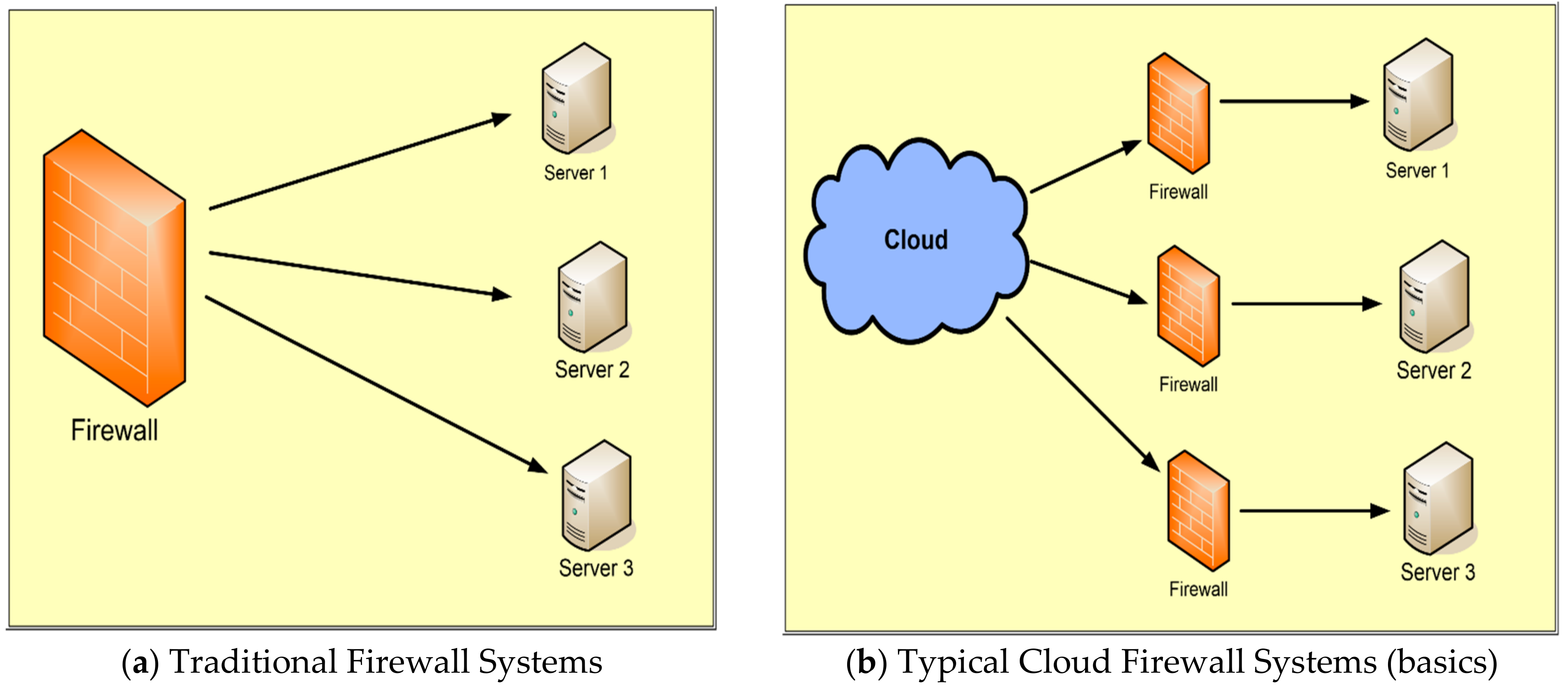
Applied Sciences Free Full Text Firewall Best Practices For Securing Smart Healthcare Environment A Review Html

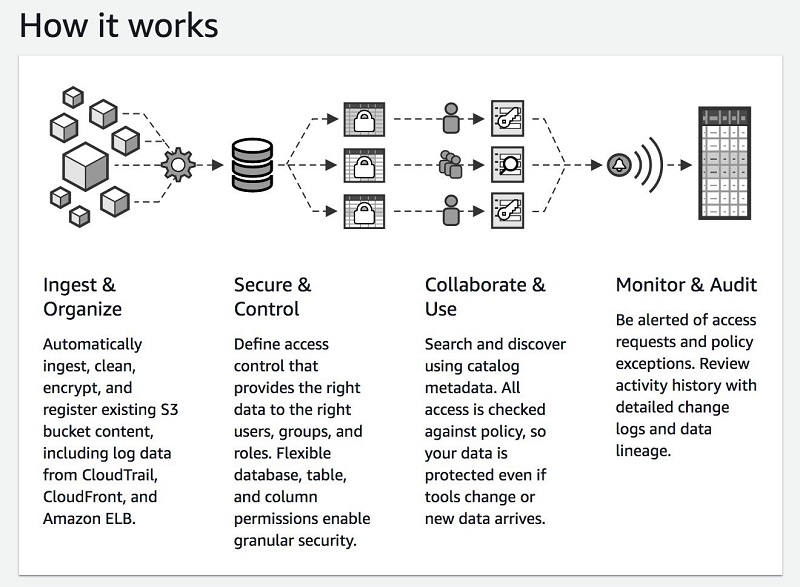
Build Secure And Manage Data Lakes With Aws Lake Formation Aws Big Data Blog
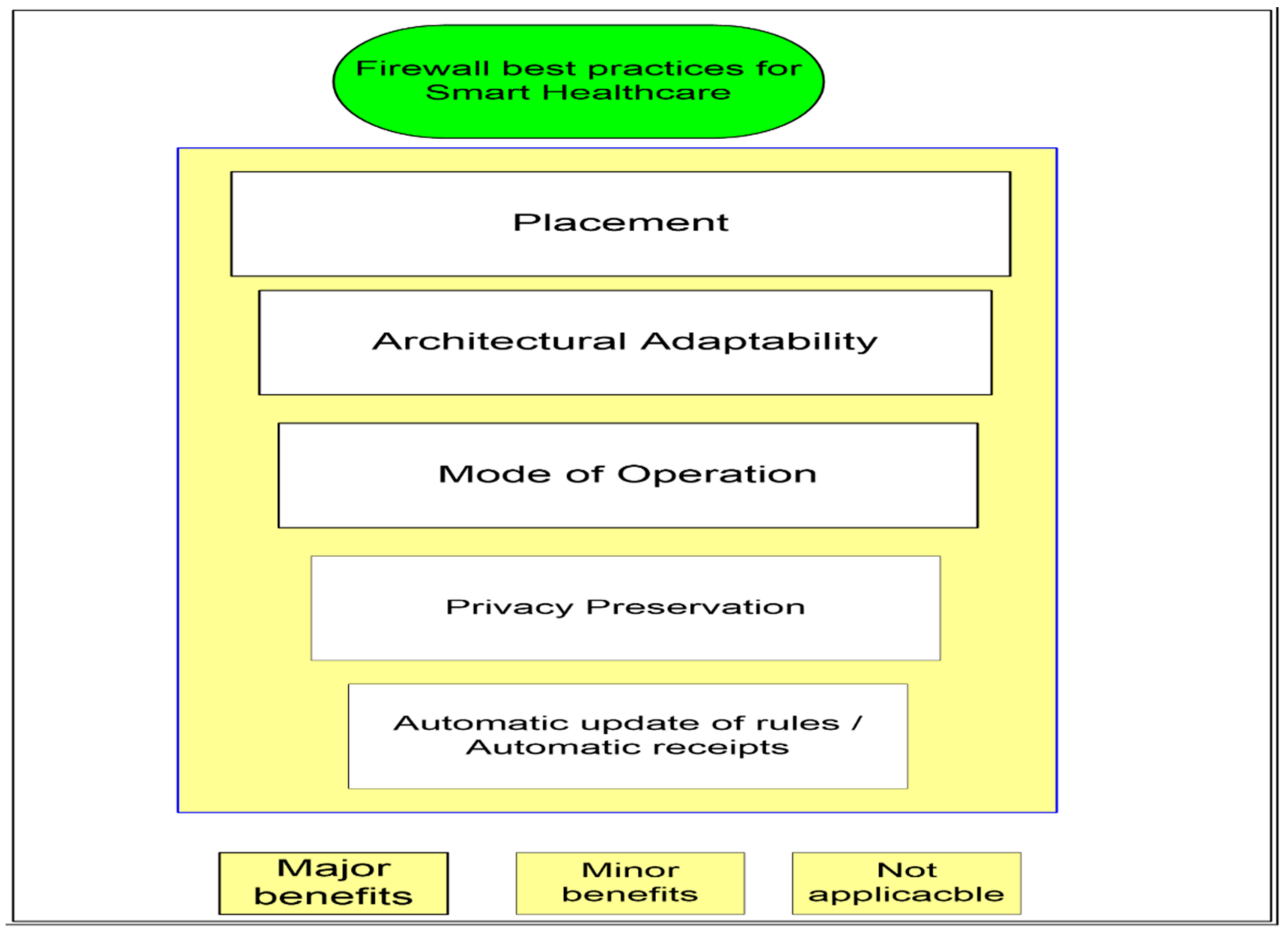
Applied Sciences Free Full Text Firewall Best Practices For Securing Smart Healthcare Environment A Review Html
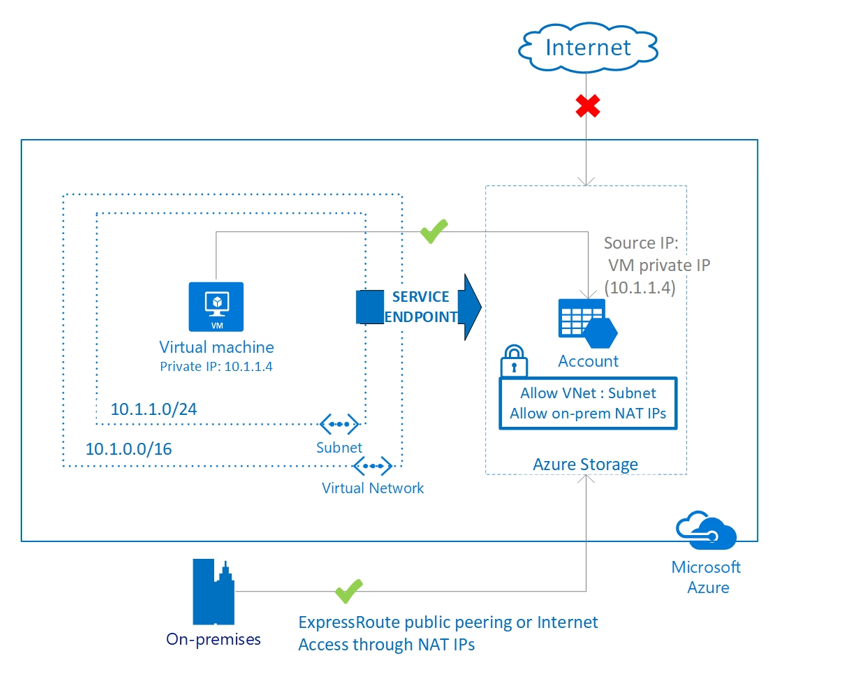
Best Practices To Set Up Networking For Migrated Azure Workloads Cloud Adoption Framework Microsoft Docs
![]()
Telework And Mobile Security Guidance

The Three States Of Data Guide Description And How To Secure Them

What Is Application Security Vmware Glossary

4 Jwt Security Best Practices Akana

Pdf Secure Multiparty Computation And Trusted Hardware Examining Adoption Challenges And Opportunities

Deploying Nginx As An Api Gateway Part 1 Nginx
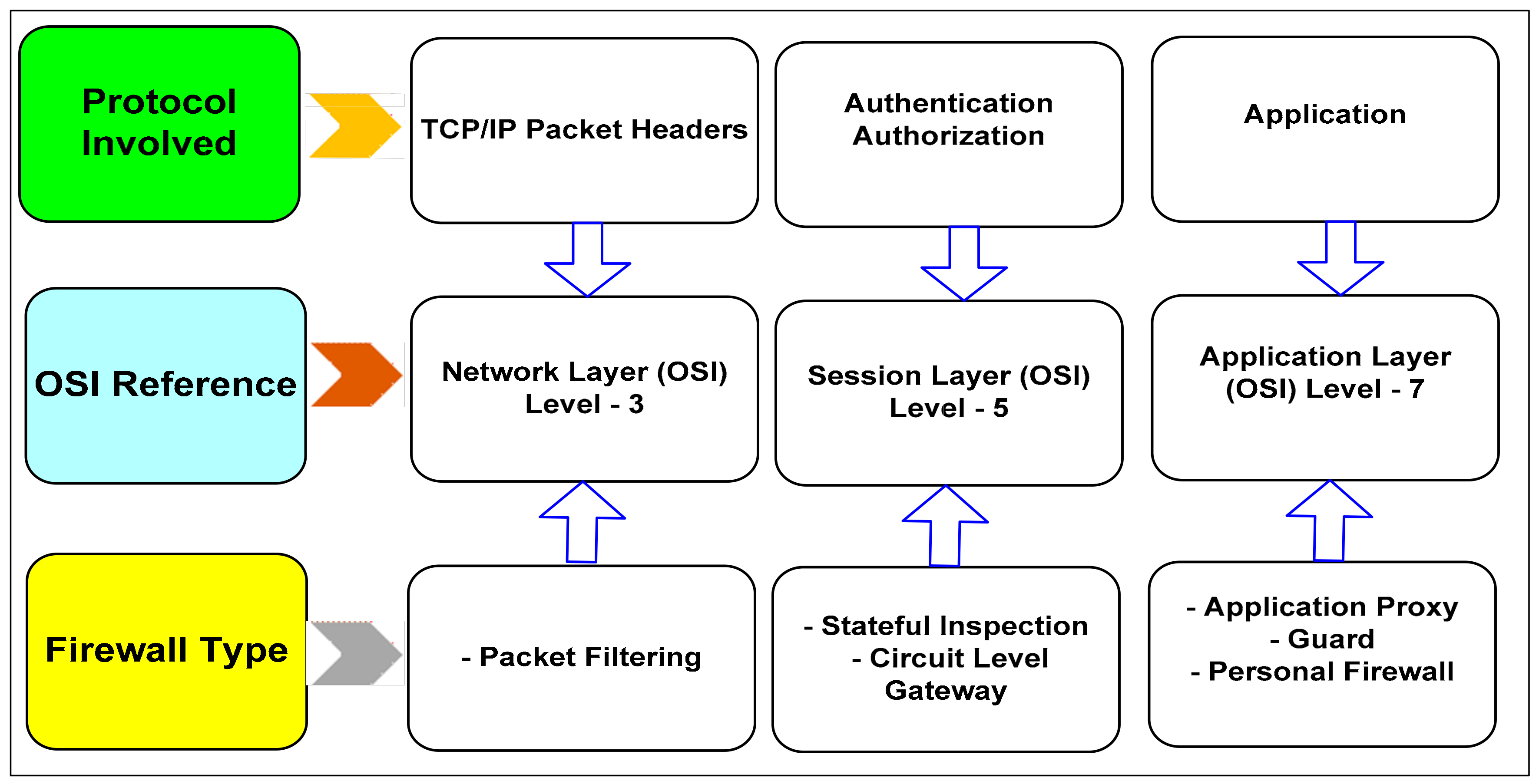
Applied Sciences Free Full Text Firewall Best Practices For Securing Smart Healthcare Environment A Review Html
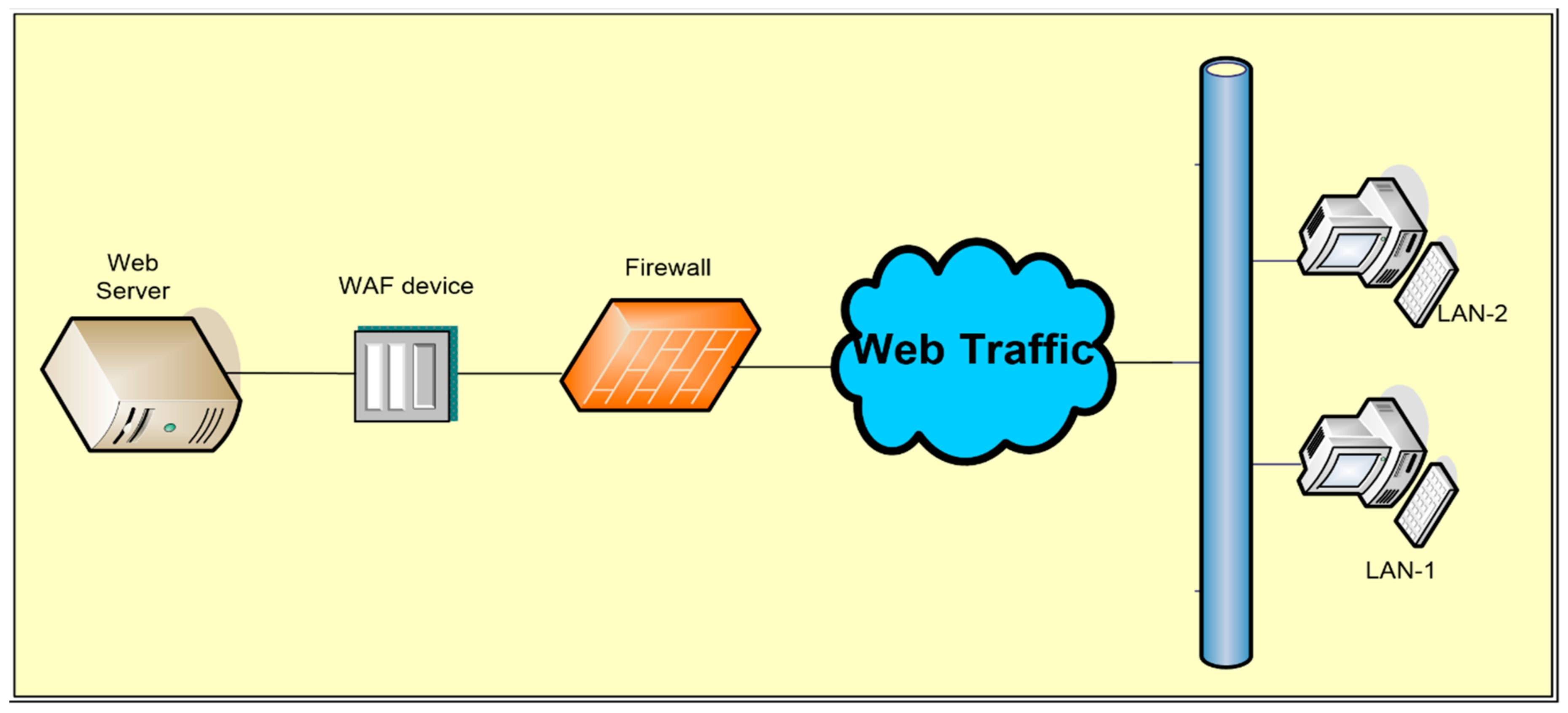
Applied Sciences Free Full Text Firewall Best Practices For Securing Smart Healthcare Environment A Review Html
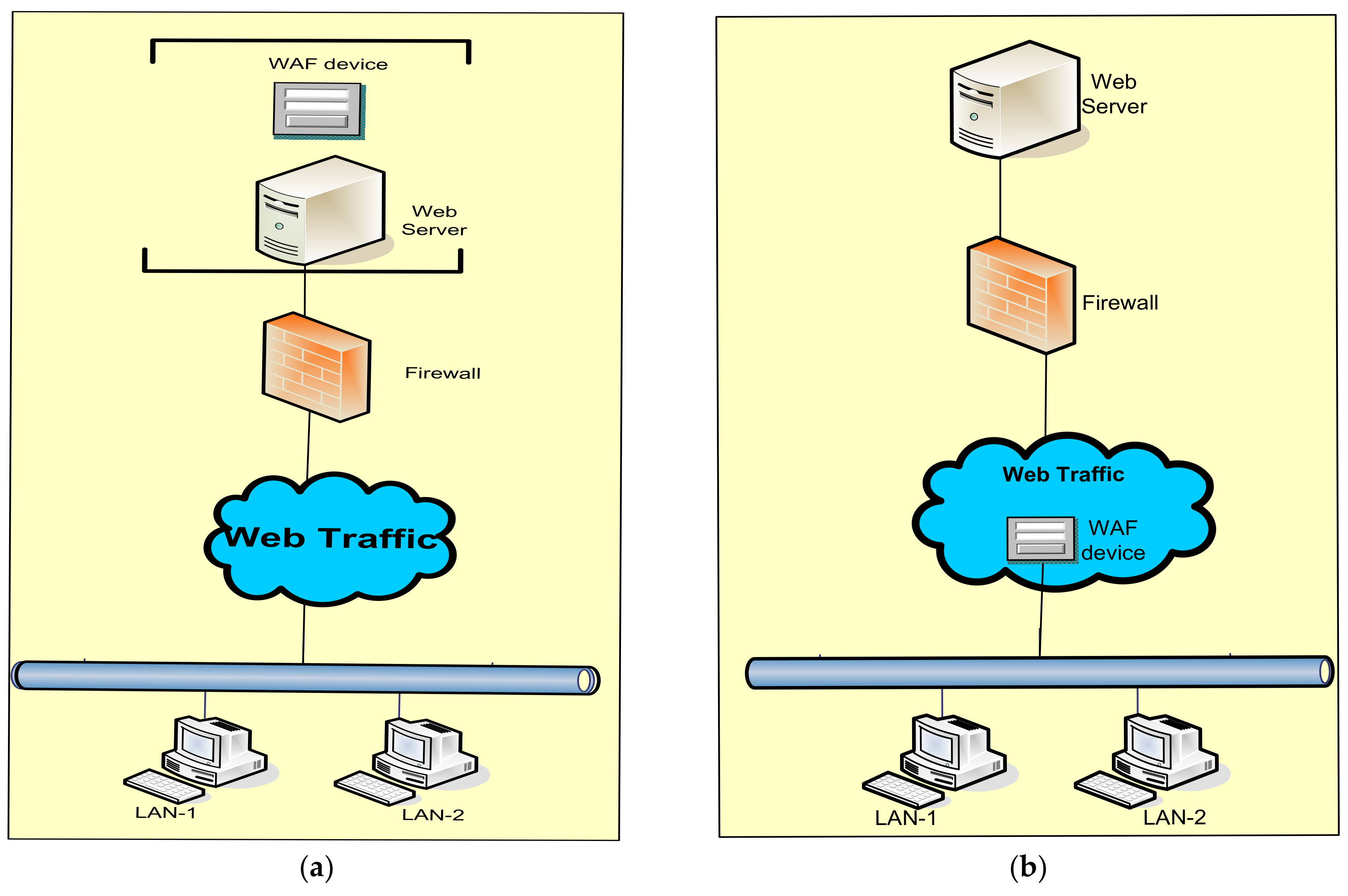
Applied Sciences Free Full Text Firewall Best Practices For Securing Smart Healthcare Environment A Review Html

Website Security How To Secure Protect Your Website

Infosec Strategies And Best Practices Packt
![]()
Telework And Mobile Security Guidance
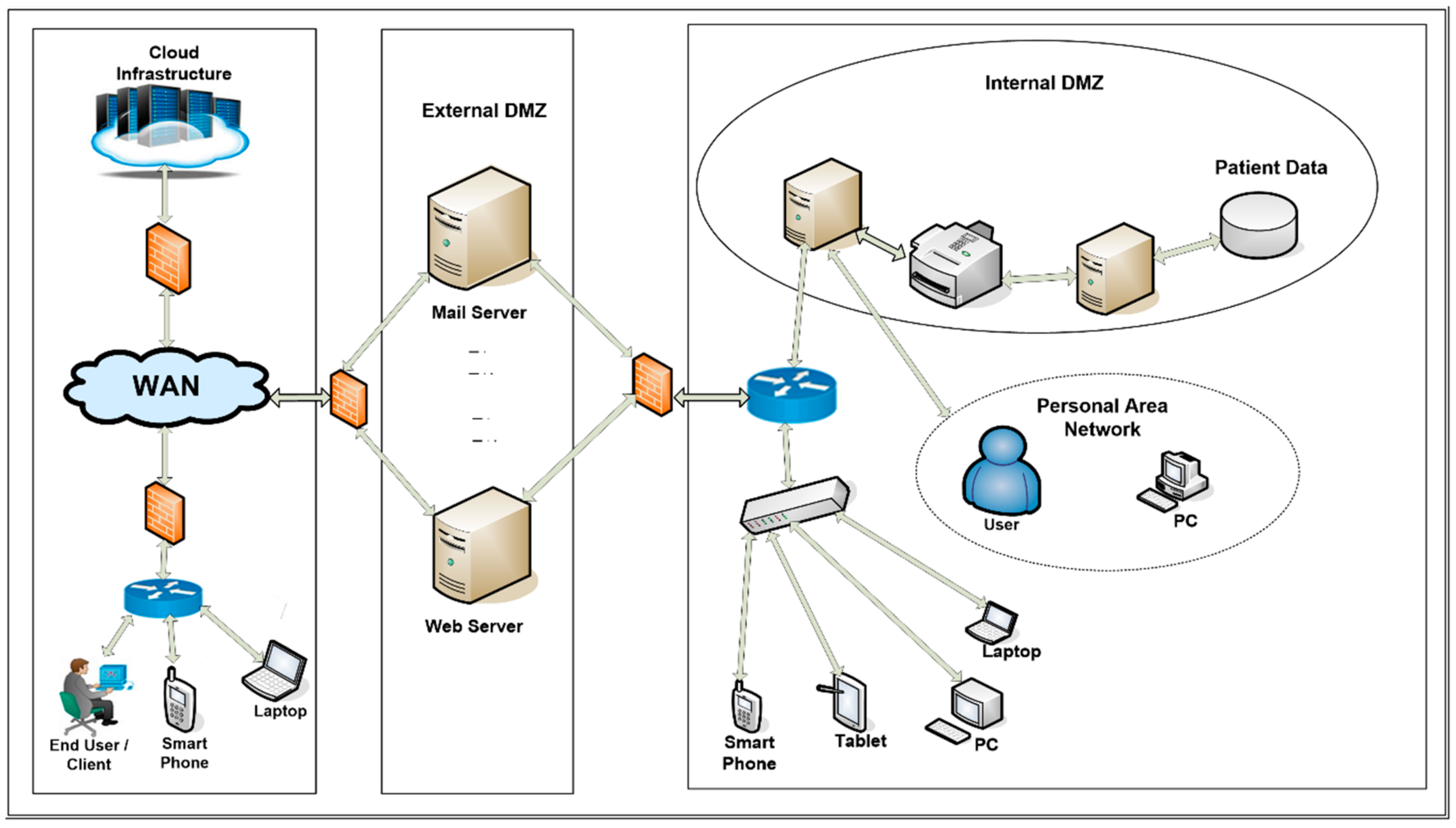
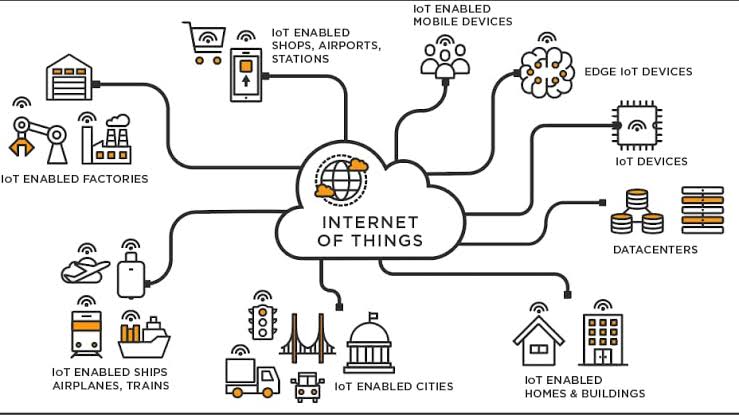
Applied Sciences Free Full Text Firewall Best Practices For Securing Smart Healthcare Environment A Review Html
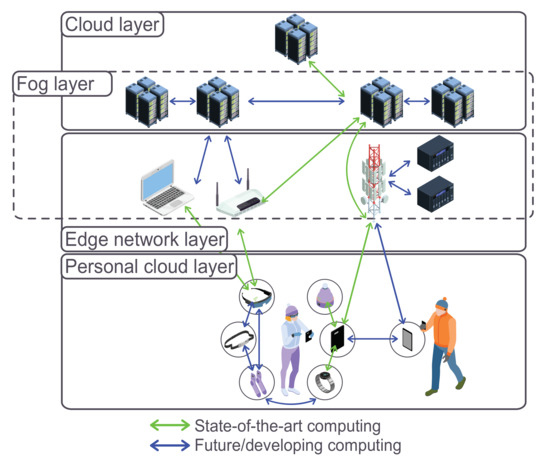
Sensors Free Full Text A Survey Of Security In Cloud Edge And Fog Computing Html

How To Tie Various Knots Prussic Knot Best Knots Rope Knots Climbing Knots
Comments
Post a Comment